A well-liked WordPress plugin could possibly be placing round two million web sites prone to assault.
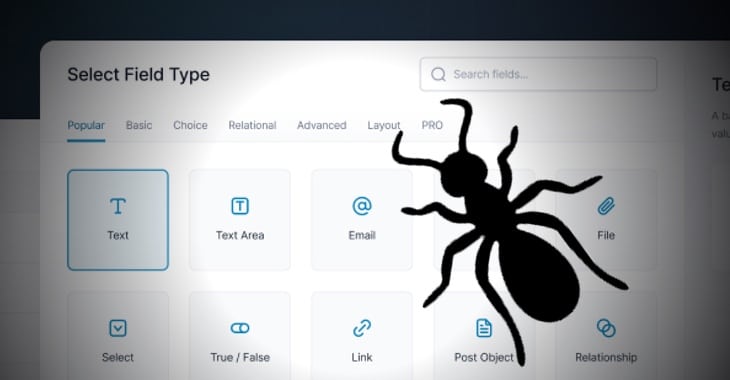
Thousands and thousands of WordPress-powered web sites are utilizing the Superior Customized Fields and Superior Customized Fields Professional plugins, which safety researchers say have been weak to cross-site scripting (XSS) assaults.
The excessive severity vulnerability might have allowed a malicious hacker to inject malicious scripts, akin to redirects, adverts, and different HTML content material into web site that will execute when customers visited the focused web site.
Fortunately, the vulnerability was mitigated considerably by the truth that it might solely be exploited by logged-in customers who had entry to the weak plugin, which means {that a} non-logged-in attacker must trick somebody who was logged in with the suitable privileges to go to a malicious URL to set off an assault.
Though that’s clearly significantly better than if the assault could possibly be initiated by anybody acessing the web site, it’s nonetheless vital that affected websites are patched promptly.
Safety researcher Rafie Muhammad found the XSS vulnerability three days in the past, and plugin developer WPEngine launched a patch yesterday.
Directors of WordPress web sites which are utilizing the affected plugins ought to guarantee they’ve up to date Superior Customized Fields to model 6.1.6 or later.

I take advantage of the Superior Customized Fields right here on grahamcluley.com, so after I first heard concerning the vulnerability I realised I wanted to patch the plugin throughout the WordPress admin console as rapidly as attainable.
Luckily, it turned out that Superior Customized Fields was one of many plugins that I’ve chosen to permit to robotically replace.
No proof has been introduced of anybody maliciously exploiting the safety gap in weak variations of the plugin, though in fact that doesn’t imply it hasn’t occurred.
Discovered this text attention-grabbing? Observe Graham Cluley on Twitter or Mastodon to learn extra of the unique content material we put up.